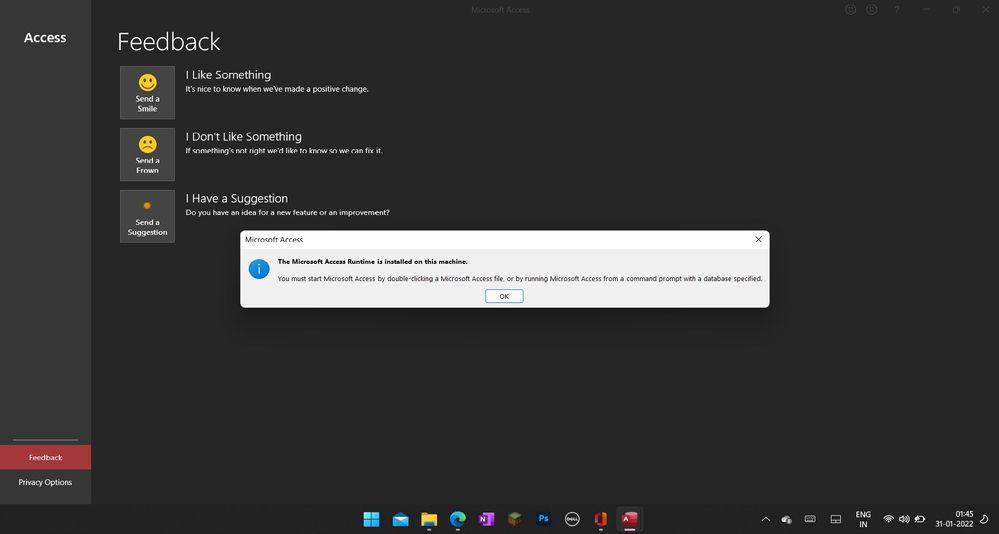
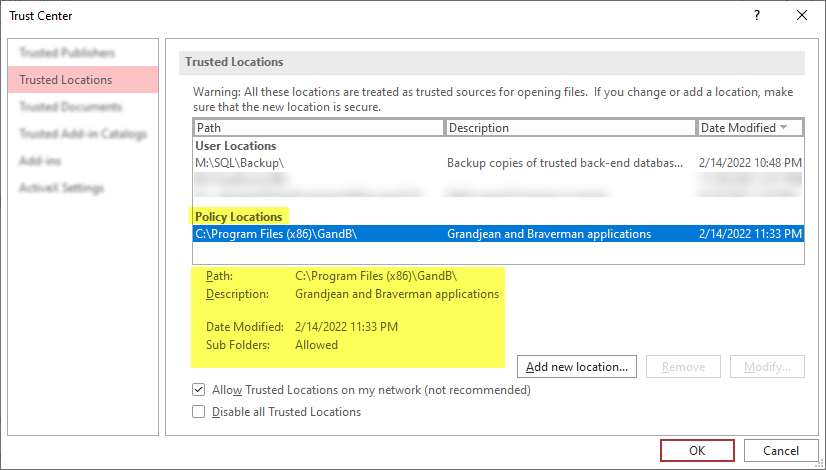
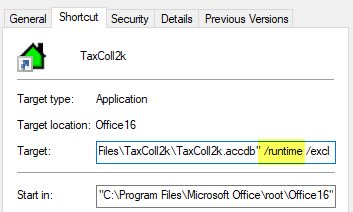
You must start Microsoft Access by double-clicking a microsoft access file error - Microsoft Community Hub
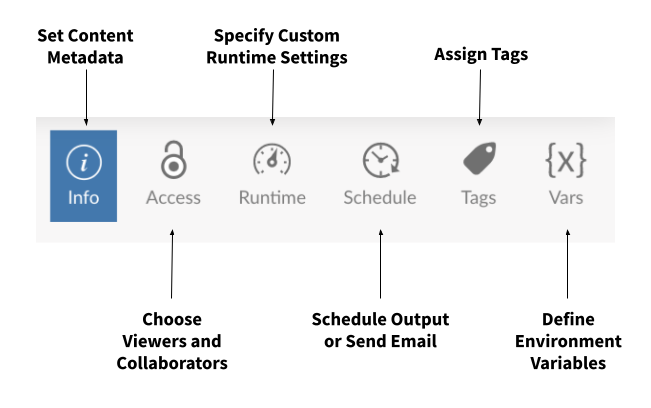
Prevent Duplicate Information from being entered into a Microsoft Access form | Database Solutions for Microsoft Access | databasedev.co.uk
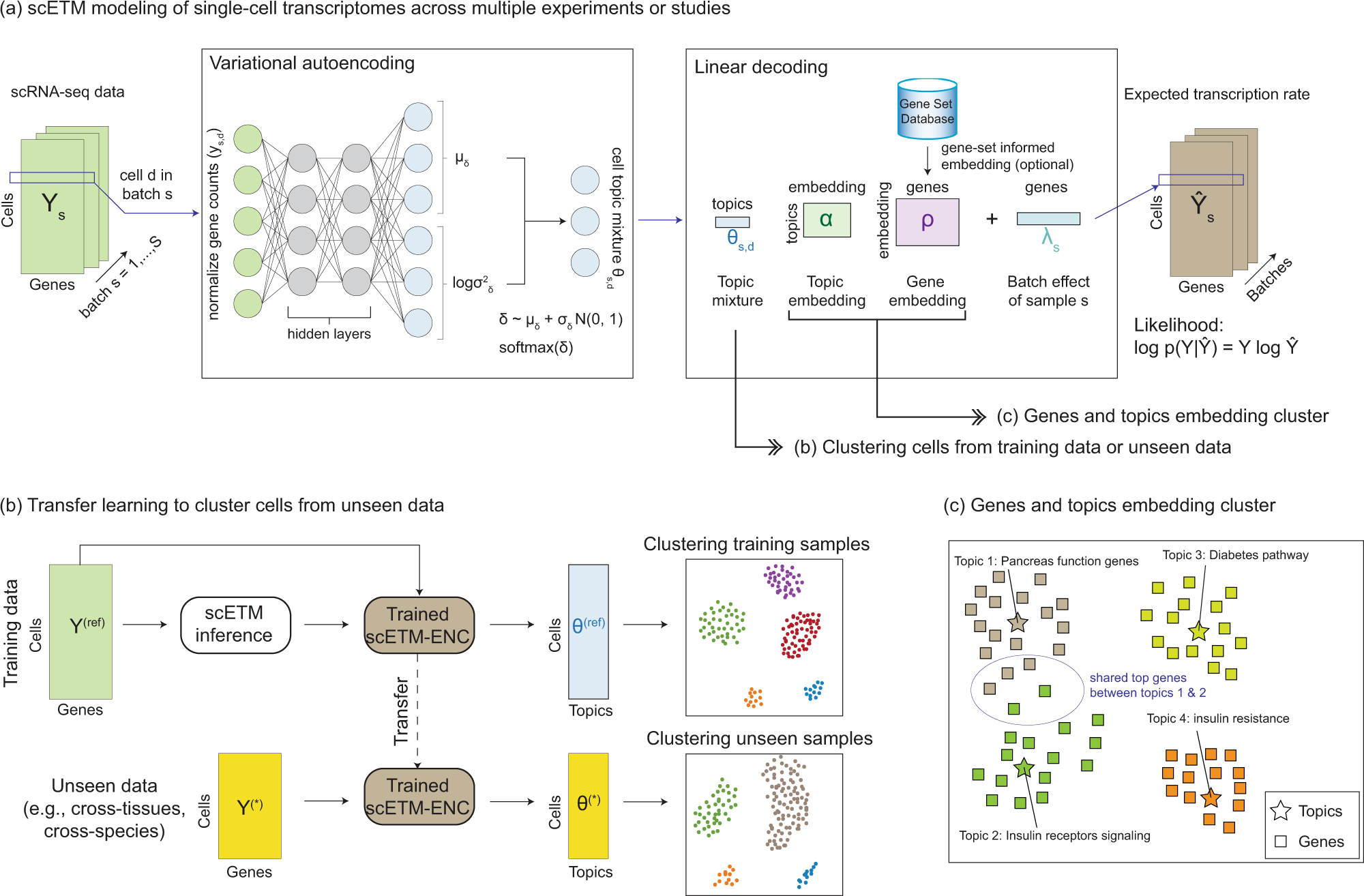
Learning interpretable cellular and gene signature embeddings from single-cell transcriptomic data | Nature Communications
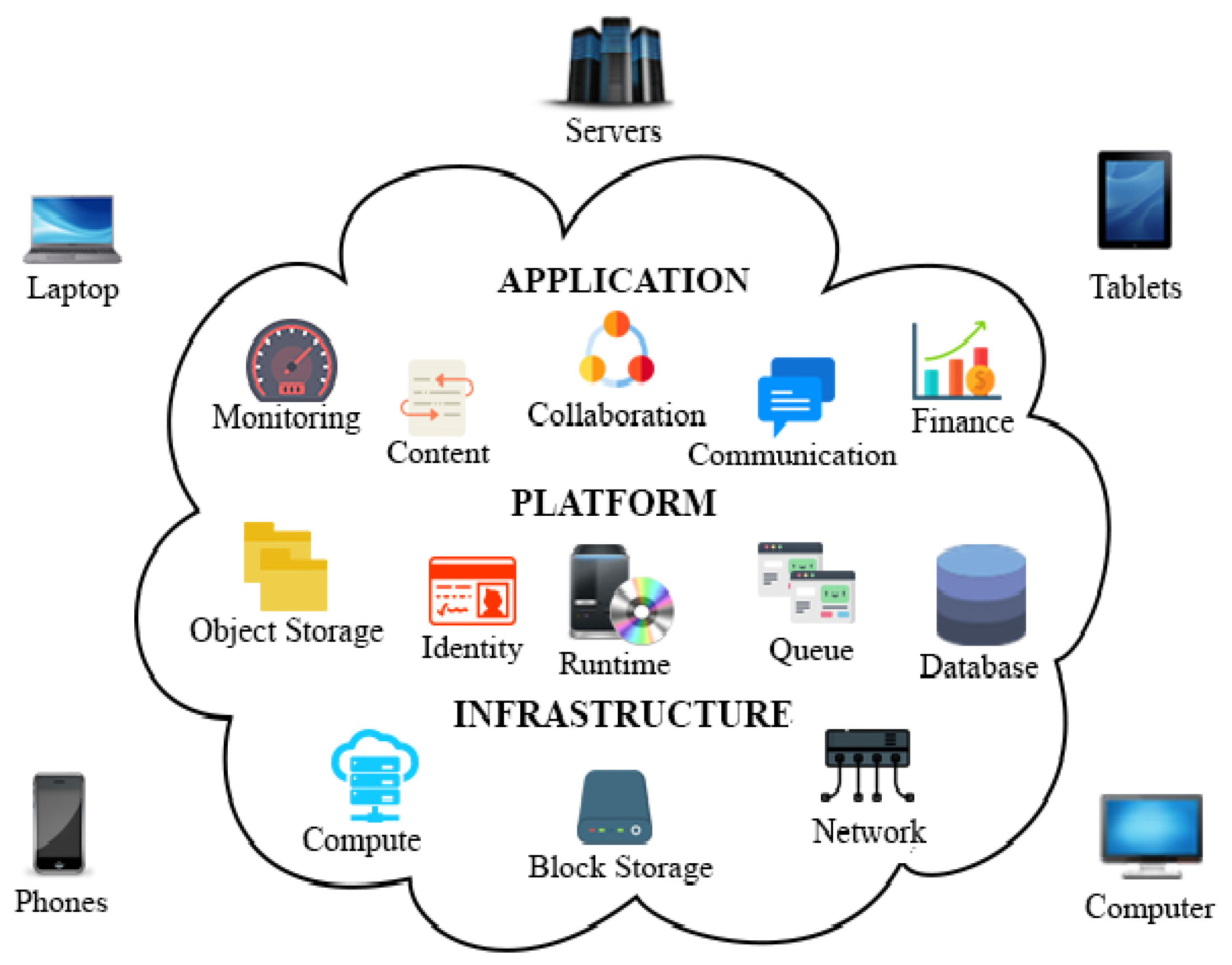
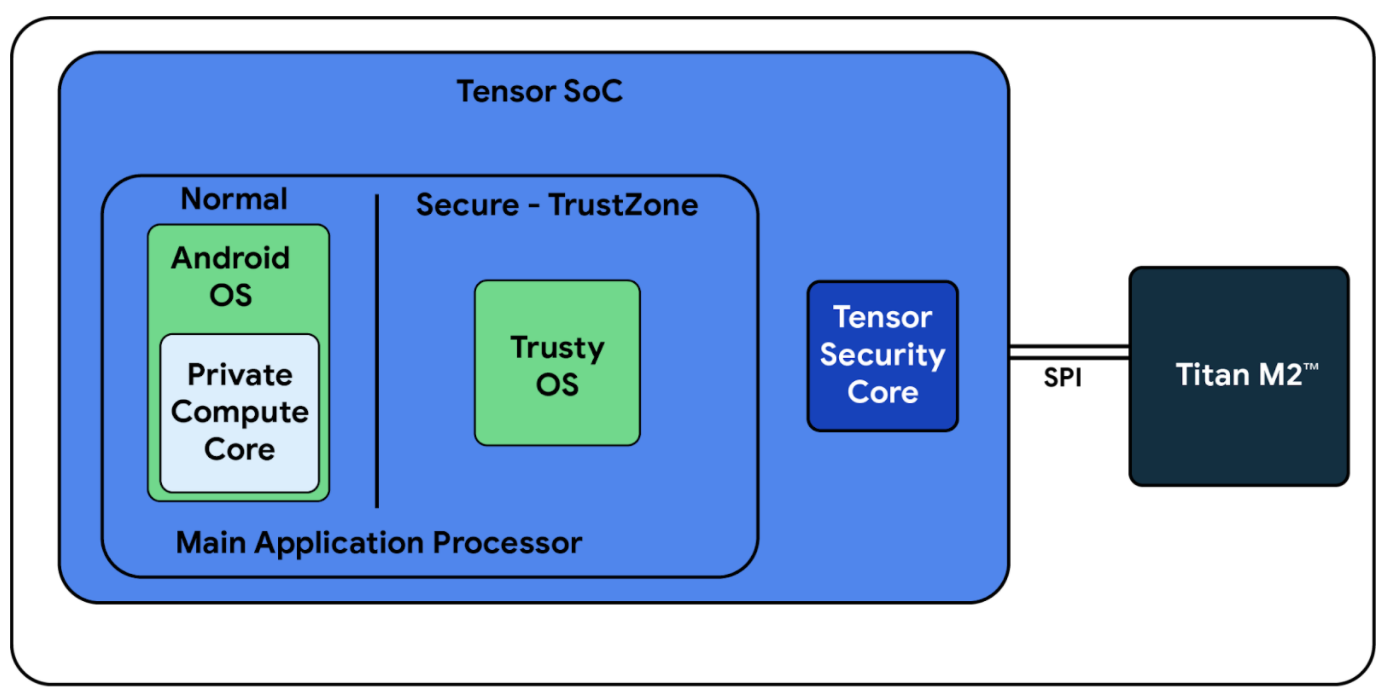
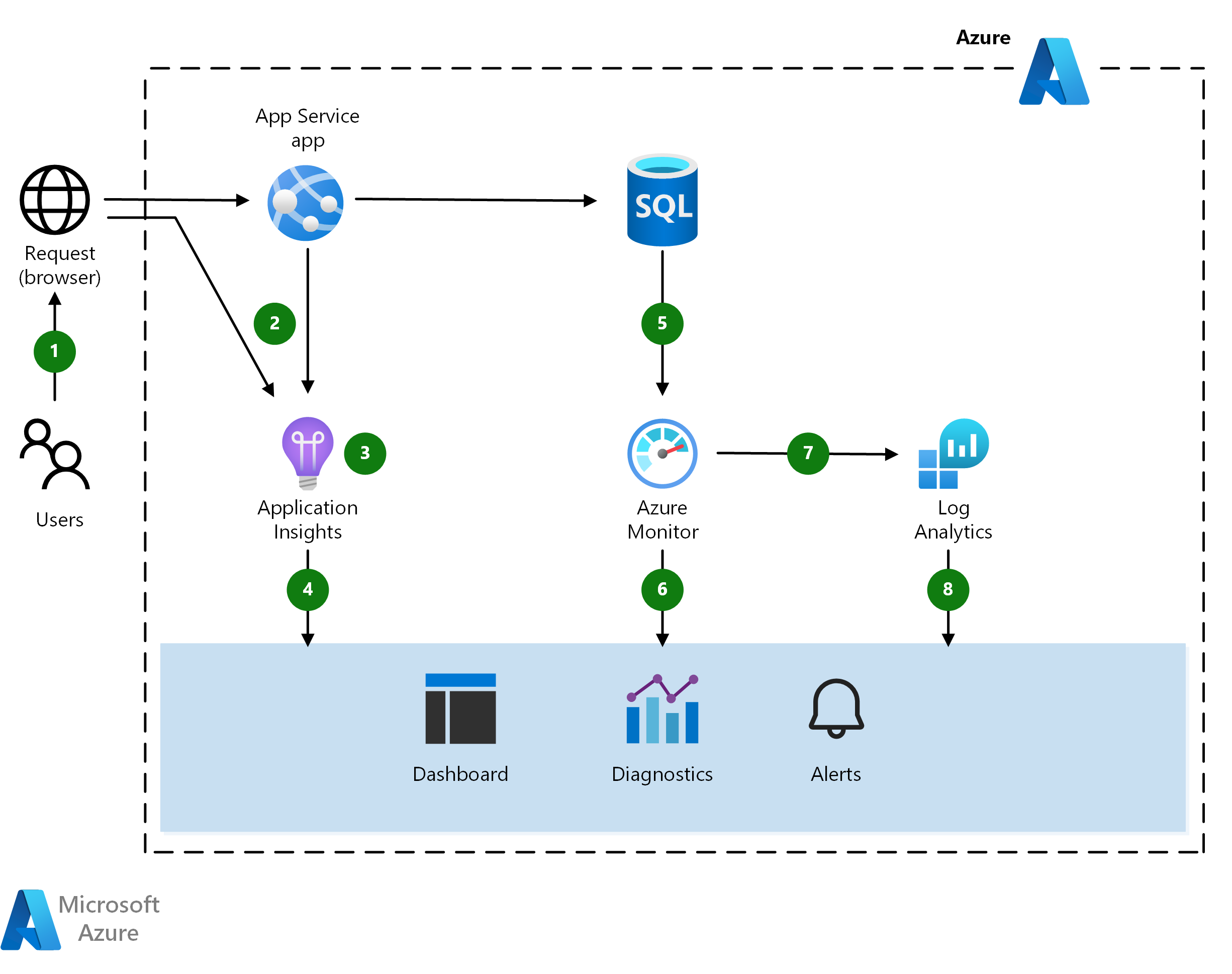
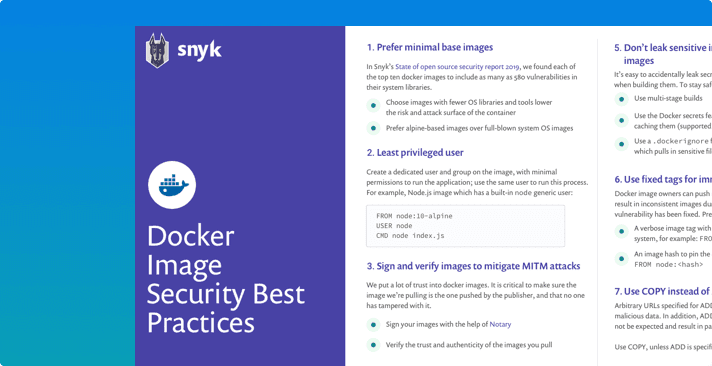
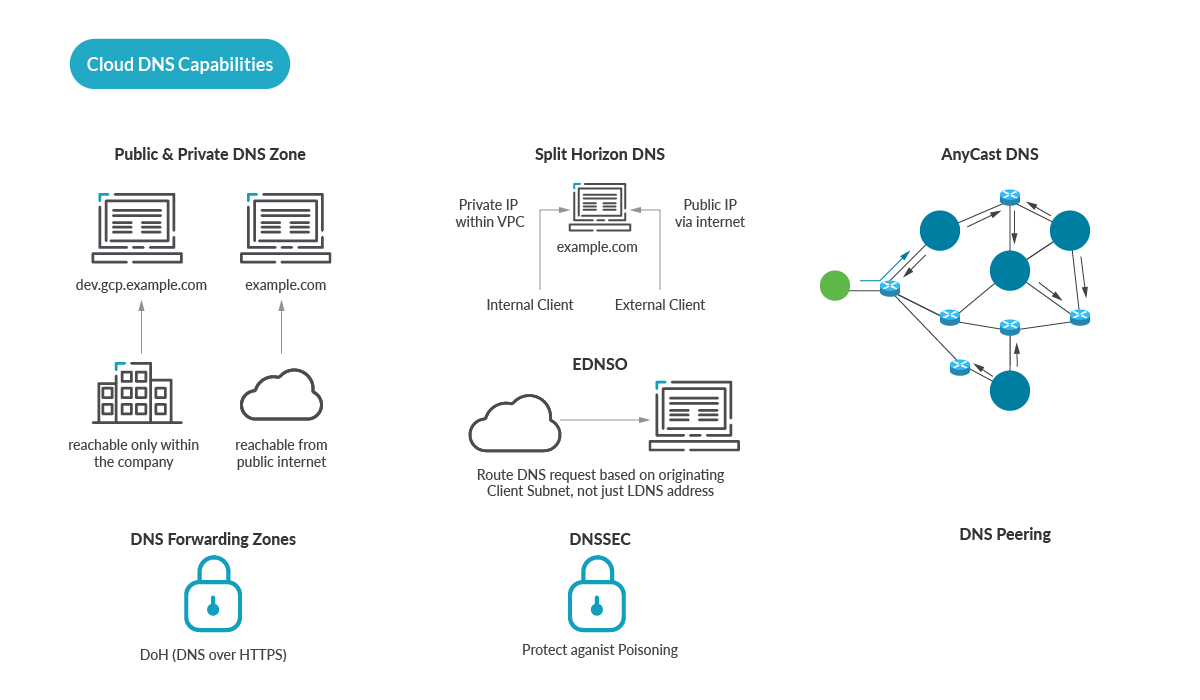
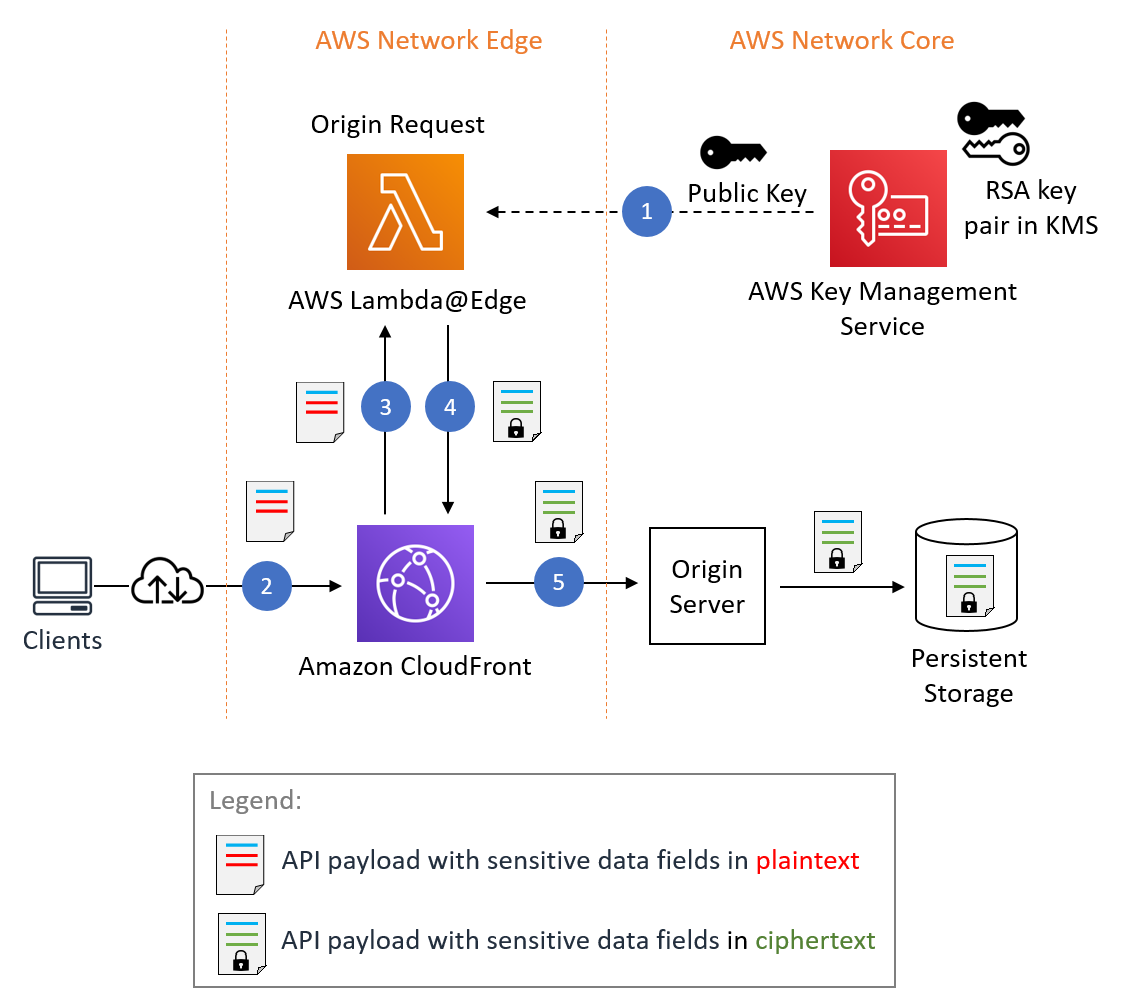
Electronics | Free Full-Text | A Survey on Modern Cloud Computing Security over Smart City Networks: Threats, Vulnerabilities, Consequences, Countermeasures, and Challenges
Prevent Duplicate Information from being entered into a Microsoft Access form | Database Solutions for Microsoft Access | databasedev.co.uk







![Fix Access Denied Errors with Ease [CMD, Hard Drive, Folder] Fix Access Denied Errors with Ease [CMD, Hard Drive, Folder]](https://cdn.windowsreport.com/wp-content/uploads/2021/11/Access-is-denied-Windows-10-1200x900.jpg)